On-Premise
Customer data centre. Zero network egress. Full perimeter control. Your hardware, your policies.
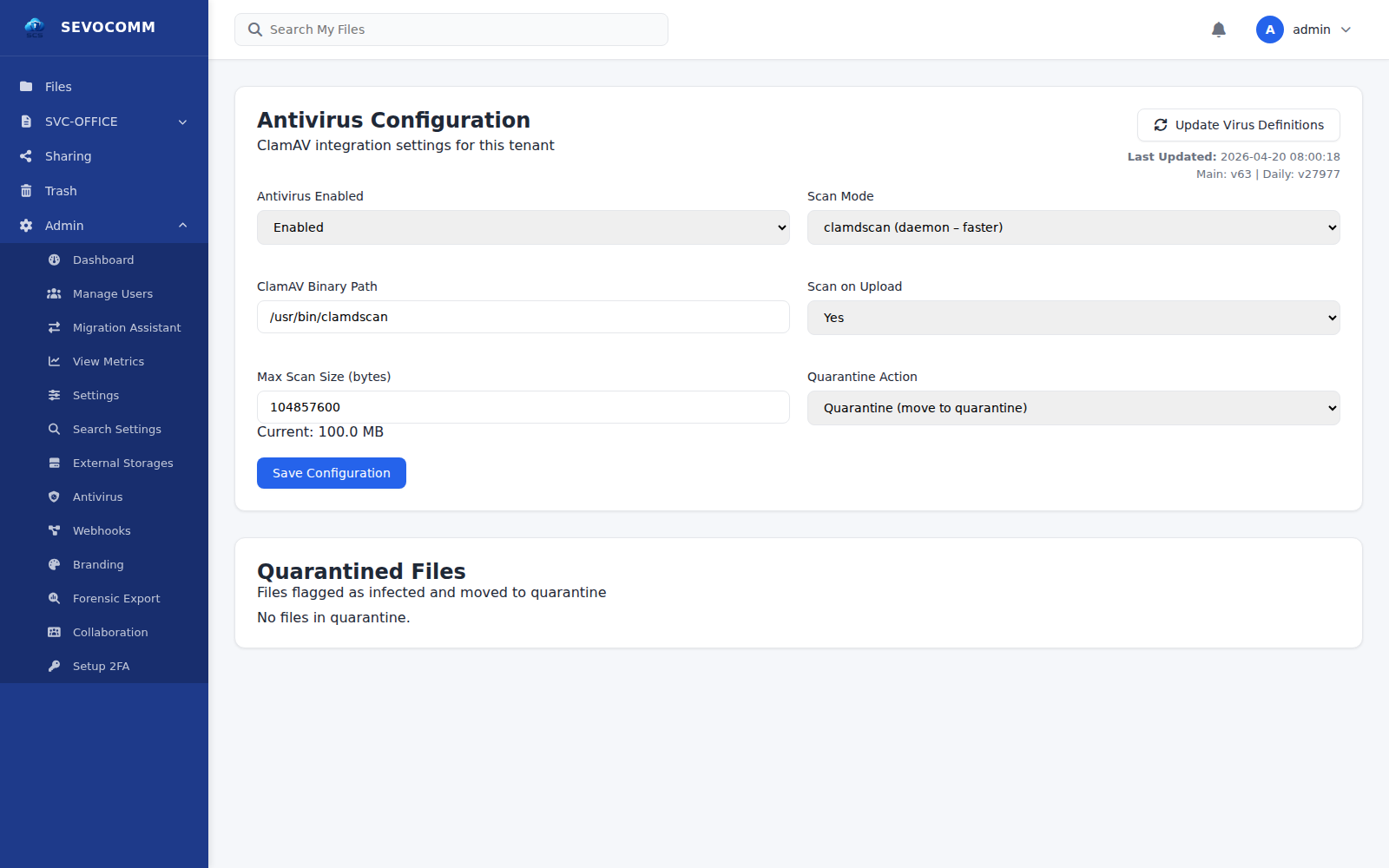
SEVOCOMM SCS is a European, sovereign secure cloud storage platform for organizations that refuse to hand their files to someone else's cloud. Client-side AES-256 encryption, customer-managed keys, full audit trails — and a deployment model you decide, not the vendor.
Scannable in seconds. Defensible in an audit.
Engineered in Europe. Aligned with strict data-protection expectations from day one.
Every file and every storage volume is AES-256-GCM ciphertext at rest — application-level plus LUKS block-layer. Zero-knowledge client-side mode available for the most sensitive data.
Customer-managed encryption keys. No vendor escrow. No silent access. Key material never leaves your boundary.
On-premise, private cloud, or fully air-gapped — identical platform, identical behavior.
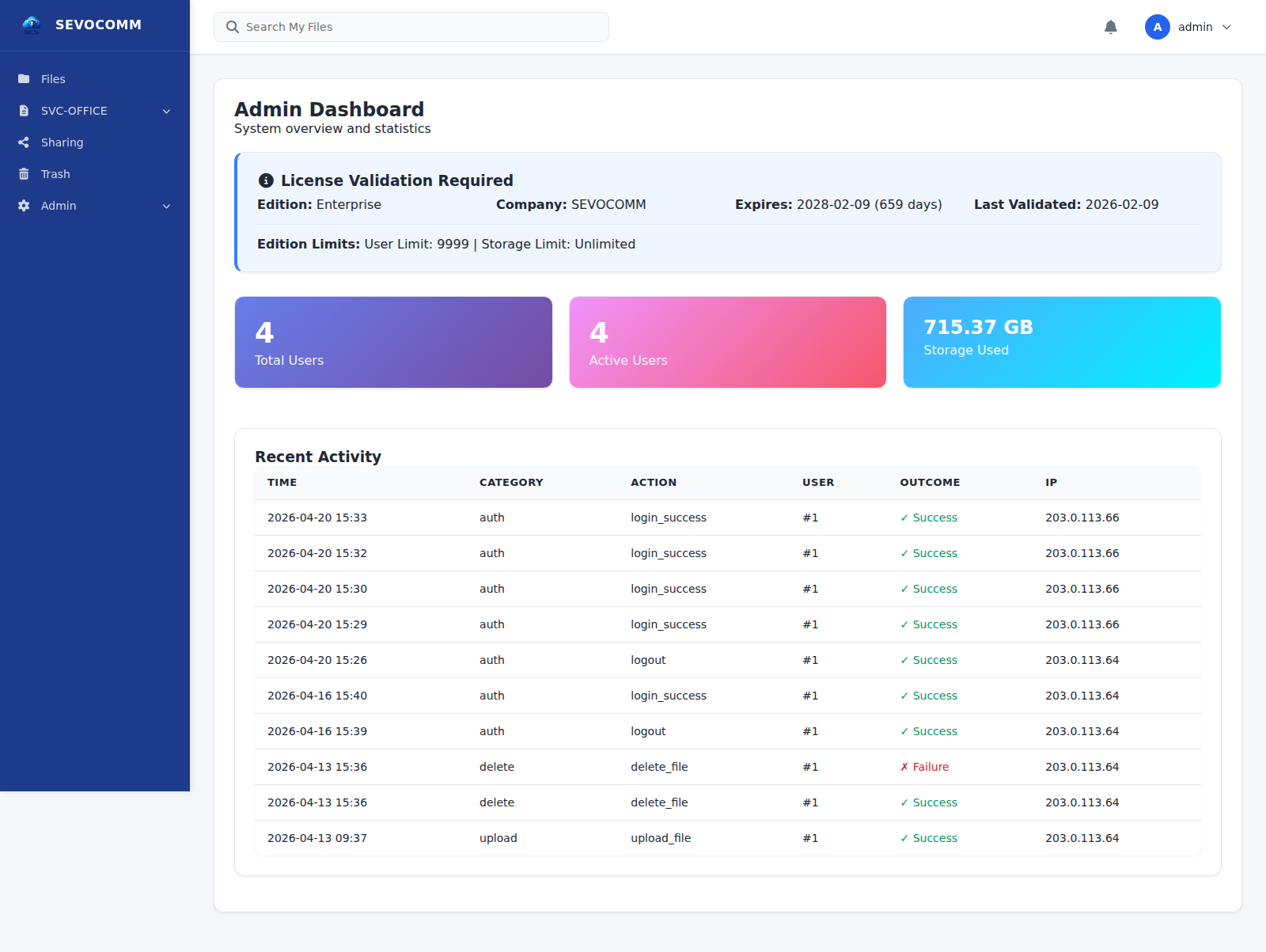
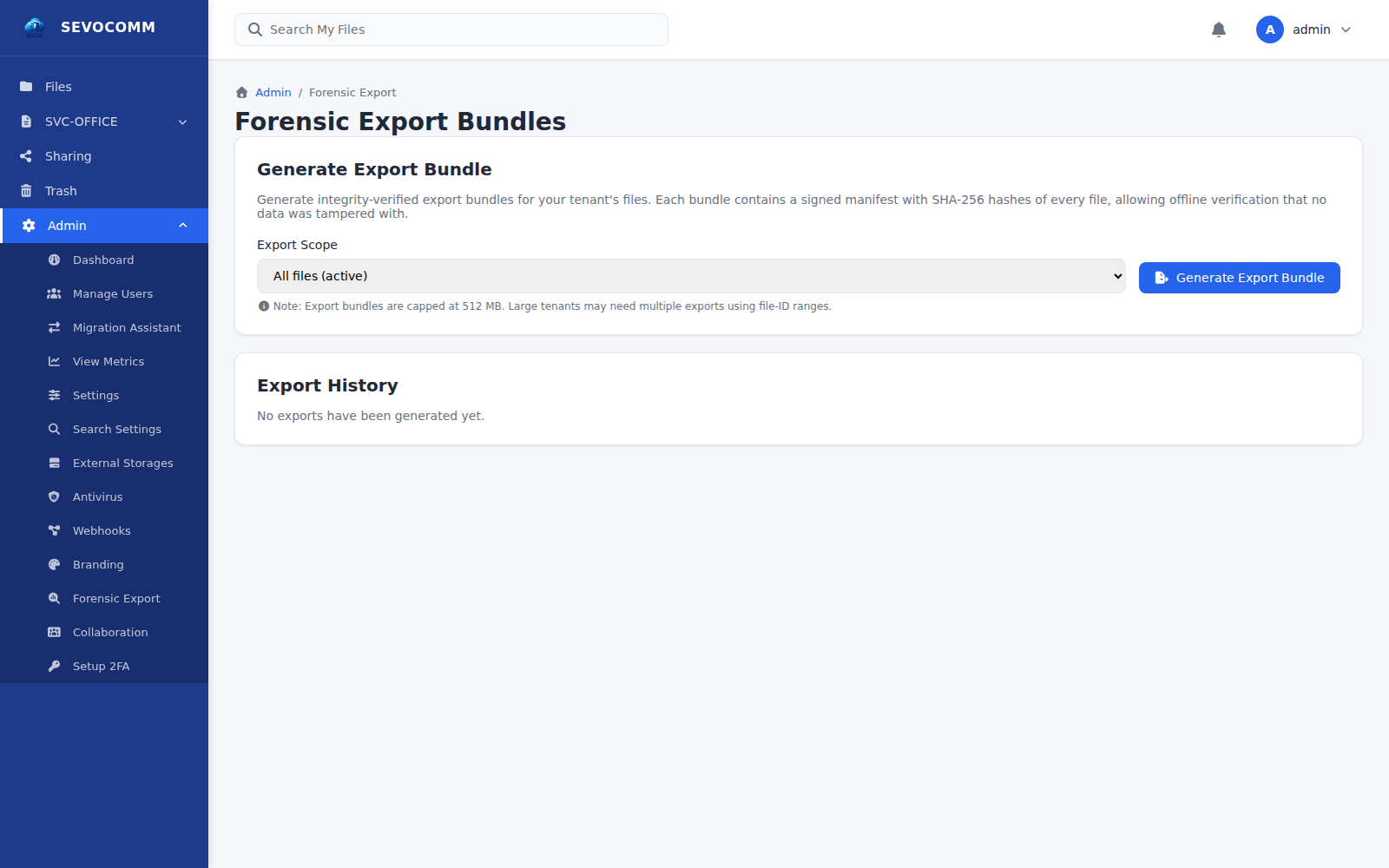
Every file access, every policy change, every admin action — captured, retained, exportable.
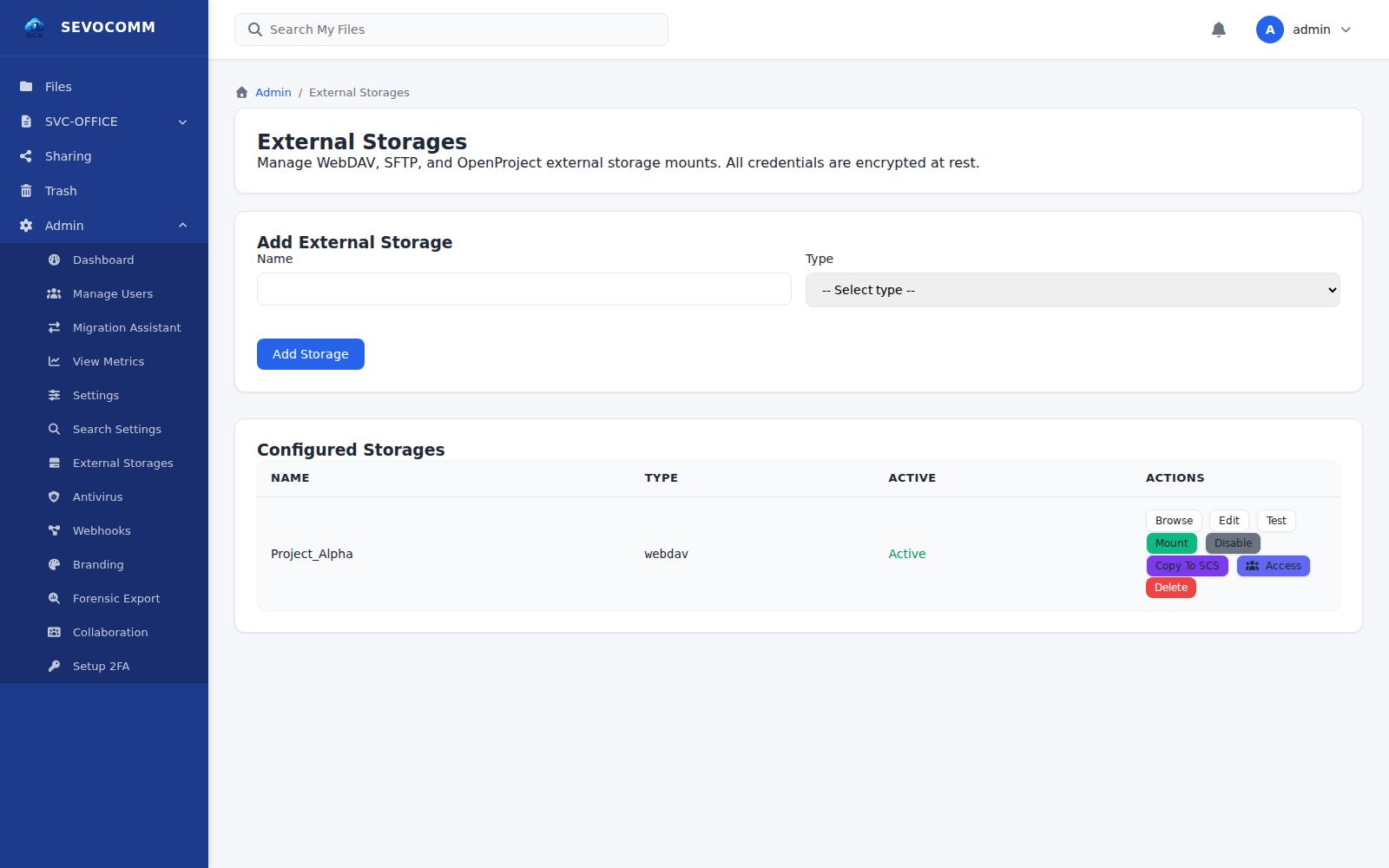
Open standards. REST API. WebDAV. No proprietary sync protocol that traps your data behind a login.
The default cloud-storage contract has quietly become: your data, on their servers, under their jurisdiction, decrypted by their keys, with access logged on a dashboard you don't own. "Private" is reduced to a marketing claim — not an architectural guarantee.
Major providers run on multi-tenant infrastructure under foreign jurisdiction. Your data coexists with data you'd never agree to share a room with.
Server-side encryption with vendor-managed keys is not privacy — it is convenience. Whoever holds the keys holds the data.
Admin access by the provider is legal, common, and rarely disclosed. You are trusting a policy, not an architecture.
Data residency expressed as a contract term — not as a physical location you control. Regulators are increasingly unconvinced.
Proprietary sync, proprietary APIs, proprietary export formats. Exit is possible — in theory. In practice, expensive and slow.
SEVOCOMM SCS inverts the arrangement.
See how deployment works →The single most important architectural guarantee of SEVOCOMM SCS: the deployment model is not imposed. It is chosen — by the customer, for the customer, with no vendor-managed layer in between.
Customer data centre. Zero network egress. Full perimeter control. Your hardware, your policies.
Dedicated, sovereign infrastructure — bare-metal or inside a VM on your own hypervisor (VMware, Proxmox, Hyper-V, KVM). No shared tenancy. Customer-managed boundary.
Fully isolated from external networks. Classified-ready for defence, legal, R&D and regulated sectors.
Multi-tenant Hosting mode. White-label ready. Multi-domain. Operator-scale provisioning with per-tenant isolation.
“Deployment is fully decided by the customer.”
— Core product principle · Non-negotiable
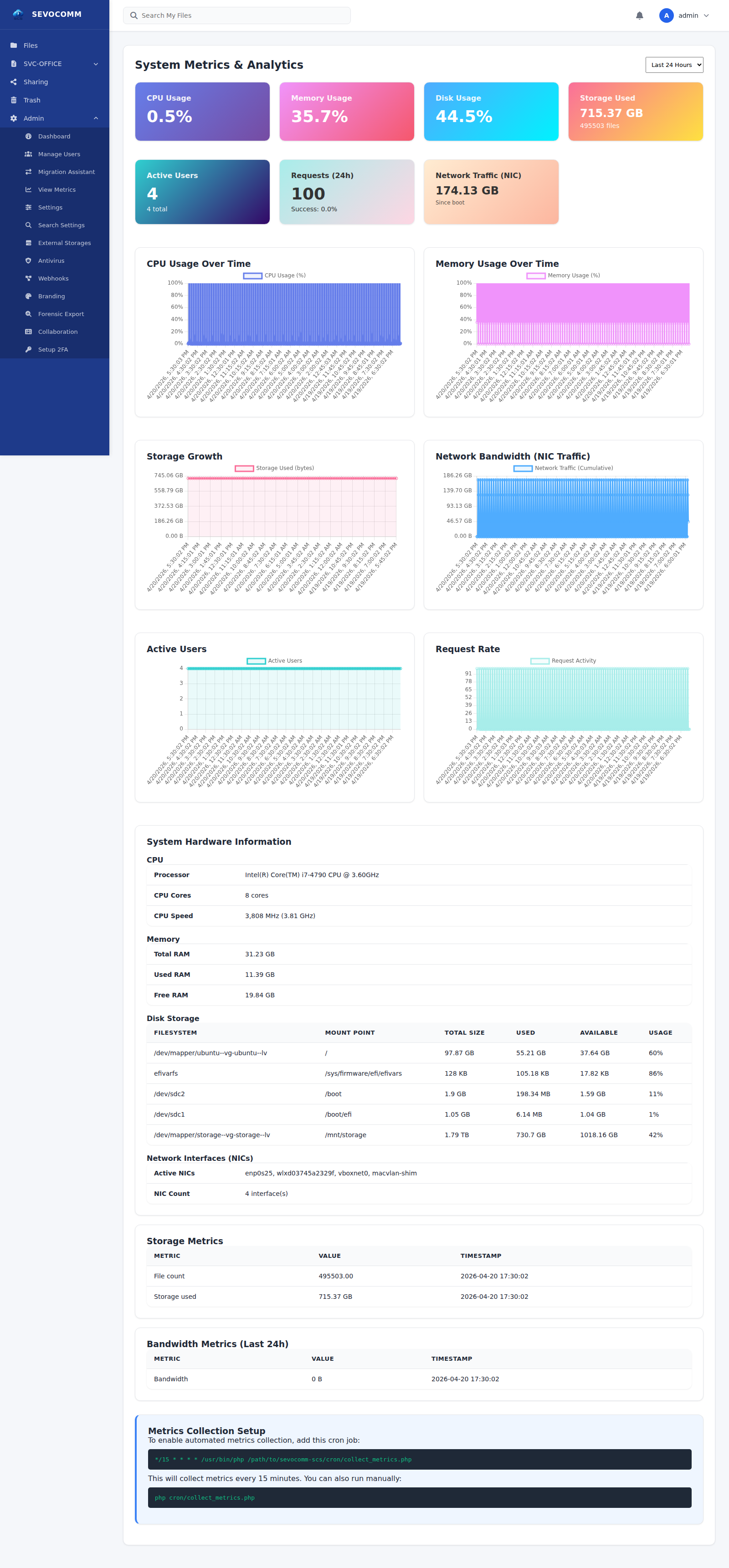
A modern secure-storage platform structured around three design principles: cryptographic privacy, operational observability, and unconditional portability — no forced SaaS layer, no vendor-held keys.
AES-256-GCM at rest, TLS 1.2/1.3 in transit, client-side encryption for zero-knowledge storage. Customer-managed keys — SEVOCOMM never sees plaintext.
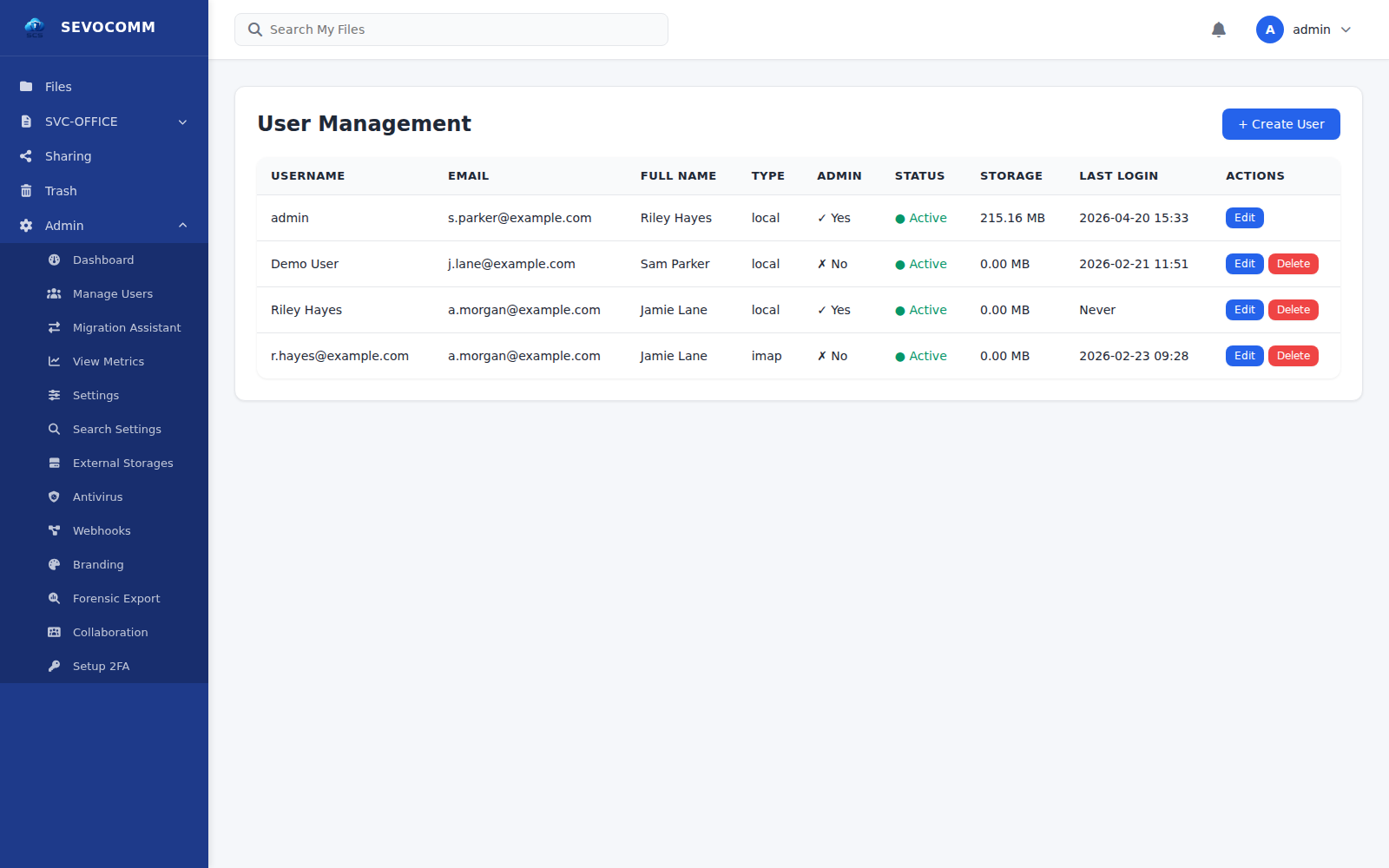
Role-based permissions, multi-factor authentication, IP allow-lists, and time-based access policies. Every permission is explicit, auditable, and reversible.
Complete file-access audit trail, retention policies, legal hold, and GDPR-grade data management — including export and erasure workflows. Evidence-ready by default.
Built-in document suite — SVC-Write, SVC-Calc, SVC-Dia — for real-time editing of .docx, .xlsx and .pptx files directly inside SCS. Secure sharing, expiring links, granular permissions, and version control — all inside your perimeter.
Automated encrypted backups, point-in-time recovery, and optional geographic redundancy. Disaster recovery is a built-in capability, not a paid add-on.
Native hand-off with SEVOCOMM MTA — oversized attachments are transparently replaced with a secure, expiring SCS link. Recipients get a clean message; the payload stays encrypted inside your SCS perimeter, never in transit as mail.
Open standards only: WebDAV, REST API, webhooks, external-storage back-ends, federation hooks, and SIEM-ready audit export. Fits any stack already in place.
SCS ships with SVC-OFFICE — a sovereign collaboration suite that opens, edits, and co-authors Microsoft Office documents without sending a single byte to Microsoft, Google, or anyone else. Files stay inside your SCS instance. Editing happens inside your perimeter.
Full-featured word processor for .docx, .odt and .rtf. Tracked changes, comments, real-time co-authoring, and pixel-faithful rendering of Microsoft Word documents. A direct alternative to MS Word — without the SaaS dependency.
Spreadsheet engine for .xlsx and .ods with formulas, pivots, charts, conditional formatting, and multi-user editing. Microsoft Excel-compatible, evaluated locally — your financial models never leave your jurisdiction.
Presentation editor for .pptx and .odp with slide masters, transitions, animations, and co-authoring. A direct alternative to MS PowerPoint — running inside SCS, never uploaded to an external cloud.
“Microsoft Office collaboration — without Microsoft.”
— SVC-OFFICE · runs locally inside SCS
A real product, running in real customer environments — including ours.
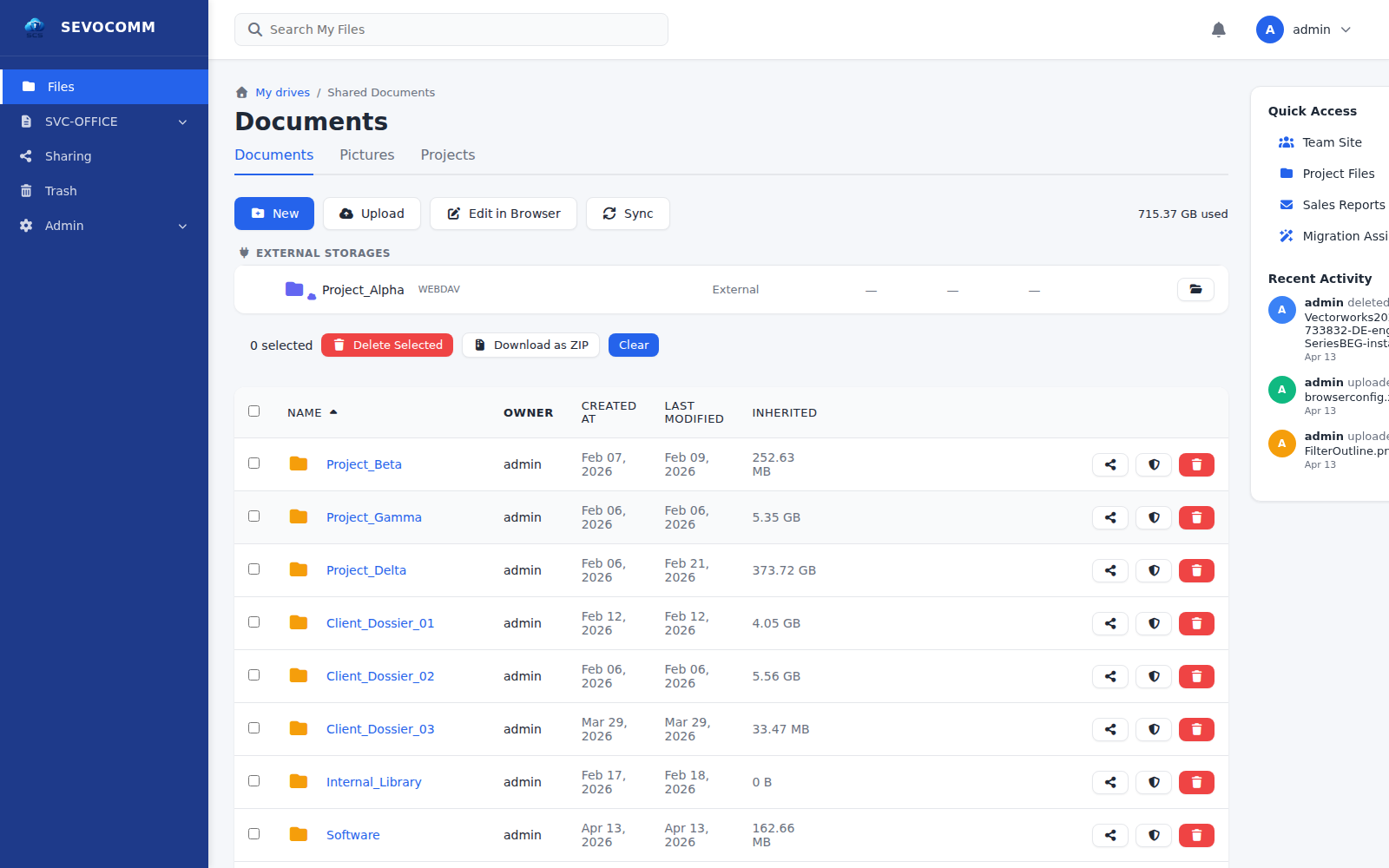
Documents, pictures, and projects — organized the way your teams already think about them. Sharing, migration, and admin all live in the same surface, under the same audit trail, behind the same encryption boundary.
Most cloud storage platforms encrypt "at rest" with keys they hold themselves. SEVOCOMM SCS is structured differently: files are encrypted on the client, with keys the customer controls, and the server never sees plaintext — ever.
The difference between “encrypted in the cloud” and “encrypted before it reaches the cloud” is the difference between a promise and a proof.
See the platform against your actual environment. A scoped, no-fluff walkthrough with our engineering team.
A built-in migration pipeline pulls existing file estates — from SaaS drives, foreign-jurisdiction clouds, legacy file servers, and competing self-hosted platforms — directly into your sovereign SCS instance. Preserves folder structure, metadata, timestamps and permissions where the source exposes them.
Full folder tree, shares and versions imported via WebDAV + native API hooks.
Deutsche-Telekom-operated storage — direct authenticated import, preserving share metadata.
Library-aware migration including versions, history and library-level permissions.
Team-folder and user-folder extraction with permission mapping into SCS roles.
Personal and business OneDrive import via Microsoft Graph — out of the Microsoft cloud for good.
Site, library and document-set migration — including version history and column metadata.
SMB-over-HTTPS file-share import — bulk transfer with integrity verification.
My Drive and Shared Drives extraction via the Drive API — Google Docs converted to .docx / .xlsx / .pptx on ingest.
Any RFC-4918 WebDAV endpoint — authenticated import with path preservation.
SSH-based file-server ingest with key-based authentication and bandwidth throttling.
Windows / Samba file-share migration over encrypted SMB3 with ACL translation.
Unix NFS exports mounted in read-only mode — safe, non-destructive source traversal.
Migration runs inside your SCS perimeter. Files are decrypted at the source, re-encrypted under your customer-managed keys, and written into SCS — nothing transits a third-party migration cloud.
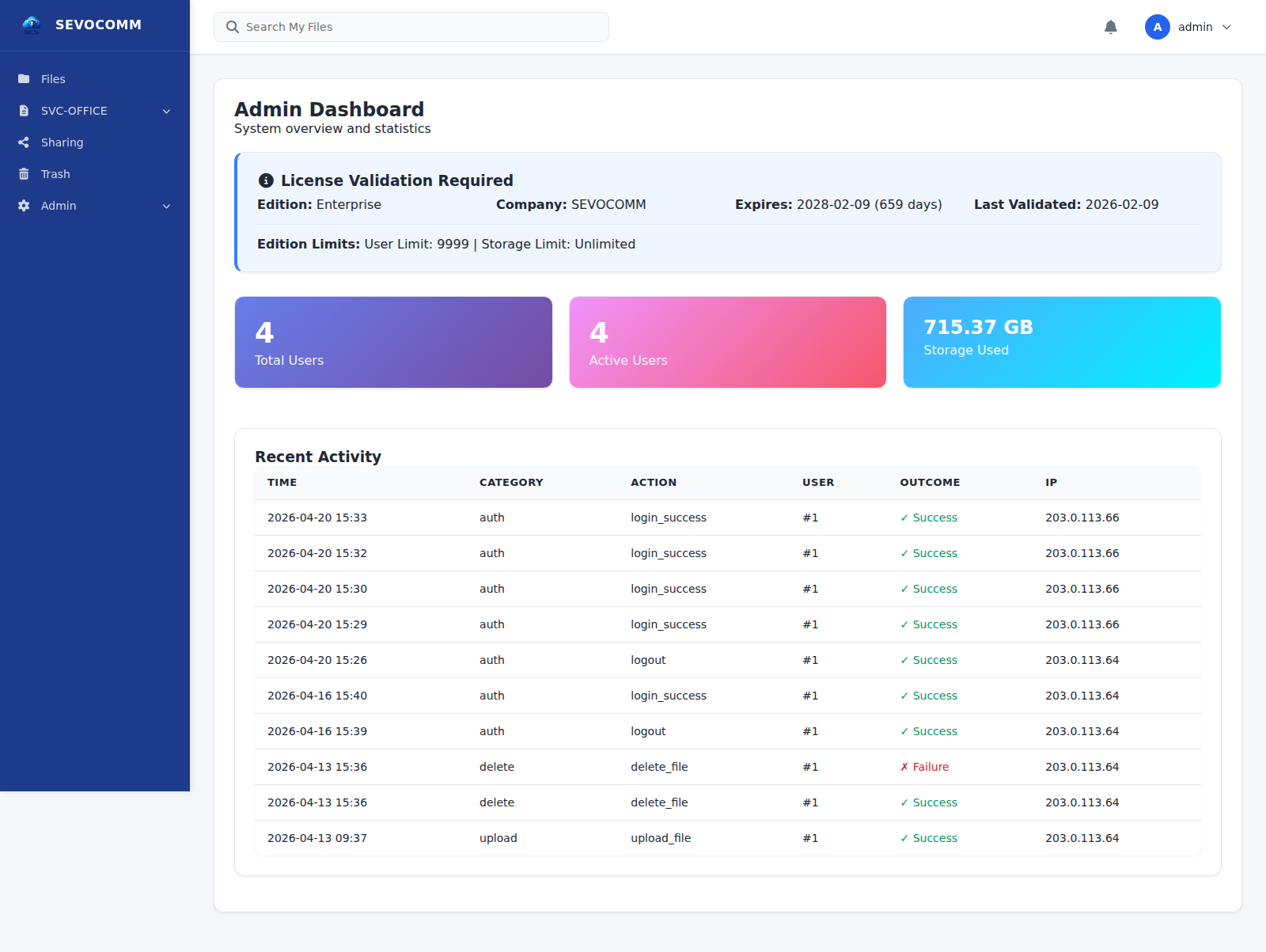
Regulated industries do not need more dashboards. They need data that holds up under an audit, a subpoena, or a GDPR subject request. SCS is built around that reality — the compliance surface is the product surface.
Three concrete, executive-level results — not features in disguise.
Own the cost model. Forecast it. Defend it.
Less exposure. Less surprise. Less dependency.
Sovereignty by architecture, not by policy.
Same platform, three operational profiles. No feature gating that forces a “move up to the next tier” conversation.
Independence, cost control, predictable deployment.
Compliance, auditability, data sovereignty, internal control.
Multi-tenant, multi-domain, white-label — operator-scale.
Legal, defence, R&D — anything that cannot leave your perimeter.
Pick the edition that matches your deployment profile — not the one that unlocks the features you should have had from day one.
Self-contained deployment for focused teams and smaller estates.
The standard enterprise deployment — for organizations that run serious infrastructure.
Full platform for regulated, classified, mission-critical, and ISP / Telco operator environments.
A compact technical summary for the people who will actually run it.
Sovereignty, encryption-by-design, and operator-held keys are not add-on features — they are the reason SEVOCOMM SCS exists. If those outcomes match your posture, the next step is a direct conversation.
A guided walkthrough of the live platform against your deployment profile and compliance requirements.
Request a demo → 02A scoped engagement with our engineering team to validate design fit, integration points, and sovereignty posture.
Book a review → 03A bounded pilot deployment — on-premise, private cloud, or air-gapped — with clear success criteria and a defined exit path.
Start a pilot →
You do not need permission to own your data.
You only need the right platform to store it.